HIGH ALERT for Scams, Phishing and Malware Attacks: Increased activity from the bad guys
In recent weeks we have identified a substantial increase in scamming, phishing, social engineering attempts, and partially compromised email accounts, targeted to clients and the broader business community. In the past three weeks, we’ve had two confirmed compromises, many close calls, and over a dozen extremely clever and targeted phishing attempts that are beyond the standard every day. Some real examples are included in this post, and note all of the examples are anonymised to protect our clients’ privacy.
With the festive season upon us, and times of high activity, workplace stress, and the remaining time before Christmas dwindling, please be extremely vigilant with email, SMS, and phone requests, as the bad guys are out in force.
Contact us if you see any:
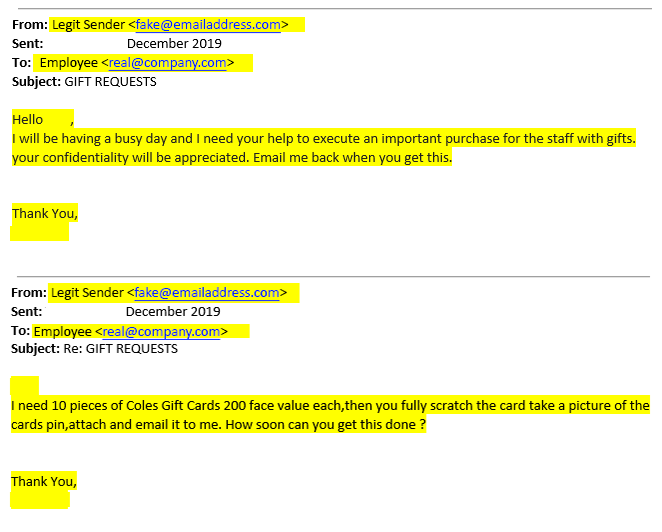
Strange requests from legitimate people – with legitimate email signatures, but the wrong email address
These are sent within the same company, but wrong email address as the sender. In most cases, the legitimate email signature has been obtained when the IT of a third party that our client works with, has been compromised, and the bad guys scrape email signatures and contact info.
Requests to quote/supply sent to suppliers from fake email accounts
We’ve seen a handful of these lately where a fake sender, impersonating an actual person complete with email signature, emails prospective suppliers and asks for a quotation. The supplier responds to the fake sender with a quote, and the fake sender replies back with a purchase order or additional information within a PDF attachment – the PDF itself then contains malware or a link to phish email account credentials.
One incident this week is particularly worrying, as it was extremely detailed and targeted to suppliers of transportable buildings/dongas – our client utilises these from time to time, and would have a legitimate interest and need to procure these. As far as the prospective supplier is concerned, it looks like a sale – then the prospective supplier gets slammed with malware or a credential compromise when they think they’ve won the sale. Harsh!
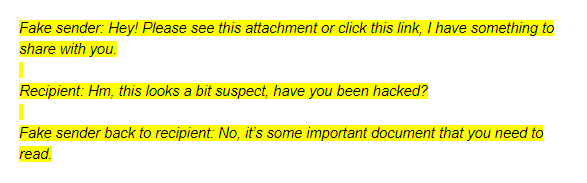
Scammers responding to you via their fake email account
We’ve also had examples where, upon mistakenly responding to a fake sender, the fake sender responds, impersonating an actual legitimate sender. An example conversation is attached. The recipient opens the attachment after being reassured that it is all legit, and then BAM! They are infected with malware or asked to log in to Office365 or Gmail, in order to obtain your legitimate account credentials. The scammers know what type of email system you use and tailor their phishing campaigns accordingly.